Fast Data Recovery
The Ransomware Recovery Experts
The Ransomware Recovery Experts
YES, we are able to recover from all types of Ransomware infections and all our work is guaranteed or your money back!
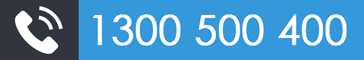
Submit a case for same day ransomware evaluation service a recent ransomware attack or to learn more about the process of ransomware recovery
Ransomware attacks have increased by 600% this year alone; impacting businesses of all sizes and more companies are falling victims to these types of cyber attacks.
Most ransomware infections occur from RDP (Remote Desktop Services) or fraudulent emails trap leading victims into opening an attachment.
Whether you’re an individual or business who needs data recovered from a recent Gryphon, Lukitus, locky, cryptolocker, cryptowall, Ceber, Arena, Aleta, Cesar, Nemesis, NM4 or the like, Fast Data Recovery has the tools, knowledge, and experience for complete ransomware data recovery, ransomware removal, and further ransomware prevention.
We have a 100% success rate on recovering data from ransomware attacks and we operate on a no data = no charge policy for peace of mind.
If this is an emergency, Please select our priority service for expedited service when submitting an online case (4-24 hours response time) or select FREE Evaluation for standard turnaround (7-14 days) at no cost.
Based on the analysis we will provide you with a fixed quote.
Part of our service is to remove the ransomware from your computer prior to restoring your data on the infected computer at no charge.
Please keep in mind that there is a possibility that your insurance policy may cover the cost of this service after the deductible is met.
WHAT IS LUKITUS RANSOMWARE?
Lukitus ransomware is part of the BTCWare ransomware family that is appending the .Lukitus extension to encrypted file names. This family of ransomware releases a new version almost every week, if not sooner, so it will be expected to see another variant released soon with a new extension.
If you are a victim of this variant you will be asked to make a payment by the hackers – DONT DONT & DONT, you will simply lose your money and it’s illegal as it falls under “Proceed of crime” not to mention you are supporting criminals resulting in more and more attacks.
Submit an online case or talk to our ransomware specialist to assist with Lukitus Ransomware recovery
HOW DO I KNOW IF MY SYSTEM IS INFECTED WITH LUKITUS RANSOMWARE?
If you are infected with malware from Australia Post, you most likely will experience some (or all of) the following:
- Pop-up message advising you that your data has been encrypted and demanding that you pay a ransom.
- Files won’t open.
- Files have been renamed with a new extension added (.Lukitus)
- Applications won’t open.
- Antivirus software is disabled.
- Computer system locked down.
- Computer system running slowly
SUBMIT AN ONLINE CASE OR TALK TO OUR RANSOMWARE SPECIALIST TO ASSIST WITH LUKITUS RANSOMWARE RECOVERY
HOW TO PROTECT YOURSELF FROM THE LUKITUS RANSOMWARE?
In order to protect yourself from the Lukitus variant of BTCWare , or from any ransomware, it is important that you use good computing habits and security software. First and foremost, you should always have a reliable and tested backup of your data that can be restored in the case of an emergency, such as a ransomware attack.
You should also have security software (please talk to us for our recommendations) as most antivirus does not give you a complete protection
Last, but not least, make sure you practice the following good online security habits, which in many cases are the most important steps of all:
- Backup, Backup, Backup!
- Do not open attachments if you do not know who sent them.
- Do not open attachments until you confirm that the person actually sent you them,
- Restrict RDP access
- Make sure all Windows updates are installed as soon as they come out! Also make sure you update all programs, especially Java, Flash, and Adobe Reader. Older programs contain security vulnerabilities that are commonly exploited by malware distributors. Therefore it is important to keep them updated.
- Make sure you have a recommended security software installed.
- Use hard passwords and never reuse the same password at multiple sites.
SOME OF THE RANSOMWARE INFECTIONS WE CAN RECOVER
- Cryptolocker / Crypt0L0cker
- Cesar
- Arena
- Lukitus
- Aleta
- Gryphon
- Nemesis
- Dharma
- Australia Post Cryptolocker
- AGL Cryptolocker
- FBI Virus
- CTB Locker
- Teslacrypt
- Virus data recovery
- Malware data recovery
- BTCWare
- Purge
- Cerber
- Blackout
- Mircop
- Locky
- Lockrypt
- Master
- Lukitus Ransomware Recovery specialist
- +++more